-
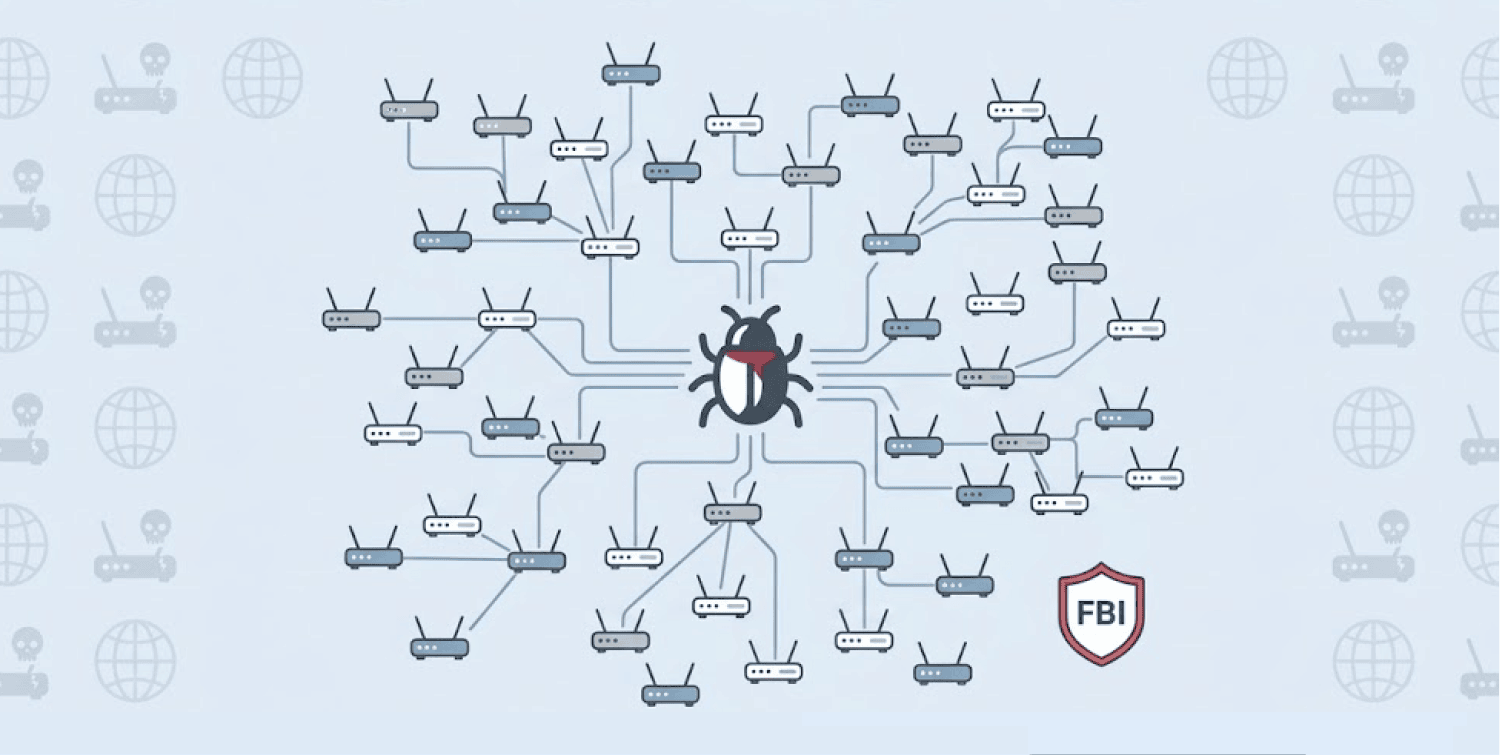
The FBI warns that cybercriminals have secretly hijacked around 369,000 home and small-office routers worldwide using AVrecon malware.
-
Cyber villains rent out these infiltrated devices as “residential proxies” via a SocksEscort service, thus making fraud appear as if it’s from regular homes.
-
The malware focuses on older routers from providers such as Netgear, TP-Link, Cisco and D-Link, because they don’t receive security updates anymore.
Hundreds of thousands of devices across the world are working for cyber thieves right now, and the owners of these devices have no idea.
The Bureau raised this alarm via its Internet Crime Complaint Center. Bad actors infect routers with a piece of AVrecon malware, which quietly runs errands for them.
Home devices to become infrastructure for bad actors
With a clever tactic, AVrecon hits routers with internet connections as well as IoT devices. The malware takes advantage of common security lapses in the most-used router providers, such as Netgear, TP-Link, Zyxel, D-Link, Cisco, Hikvision, as well as MikroTik.
The malware looks for remote code execution loopholes as well as command injection bugs in particular. Once it locates any, AVrecon sets itself up silently while the router keeps working normally, adding the infiltrated device to a massive botnet.
Cybercriminals then take these infected home and business IP addresses and package them up. They sell access to them through a long-running service called SocksEscort.
These stolen connections work as “residential proxies.” This means criminals can route their malicious activity through your home internet connection. To anyone watching, the fraud looks like it’s coming from an ordinary residential address of yours.
The scale and impact of the operation
The FBI’s investigation reveals staggering numbers. Criminals have compromised around 369,000 devices across approximately 163 countries. The United States counts among the affected nations.
Criminals use these residential proxies for a wide range of illegal activities. The FBI’s alert lists several crimes enabled by this infrastructure. Banking fraud sits at the top of the list. Romance scams follow closely behind. The proxies also facilitate ad fraud schemes and password spraying attacks.
Attackers also exploit website vulnerabilities through these hijacked routers. They carry out various forms of digital marketplace fraud and other online scams. The residential IP addresses give criminals a perfect disguise. Security systems struggle to distinguish between legitimate home traffic and criminal activity.
The operation has been running for years. AVrecon has infected devices since at least 2020, giving criminals a long time to build this massive proxy network. The service continues operating today, renting out access to unsuspecting victims’ internet connections.
EOL routers to create room for exploitation
The FBI highlights a critical problem in its warning. Most of the affected devices are older versions that producers group as EOL or “end-of-life.” As such, the firms no longer provide security patches or updates for these devices.
This creates a perfect storm for exploitation. Security researchers discover new vulnerabilities constantly. When a router reaches end-of-life status, those vulnerabilities stay open forever. Criminals know this. They specifically target these abandoned devices because no patch will ever fix them.
The same principle applies to Android phones running outdated operating systems, a key factor in the proxy network Google shut down, underscoring why keeping all devices updated is critical for preventing them from being absorbed into criminal botnets.
Thus, security researchers admonish users to check their router model and EOL status. The router’s firmware should remain updated, and automatic updates should remain active.
Users should change the default admin access to the router. Replace it with a strong, unique password. Also, monitor for fishy activities. Most routers show connected devices via their admin panel. Strange connections to the network could signal compromise.
The AVrecon botnet shows how cyber villains turn even everyday devices into weapons. Your home router is no longer ordinary equipment for internet connection. It can facilitate fraud and other nefarious actions.