The internet you use every day is only a fraction of what’s actually out there. Hidden just below is an enormous, unseen space called the deep web. An area that isn’t indexed by traditional search engines like Google or Bing. Today, as concerns around privacy, cybersecurity, and digital surveillance continue to grow, understanding what the deep web is and what it isn’t has become more important than ever.
Contrary to popular belief, the deep web isn’t inherently dangerous or illegal. It includes everyday content like private databases, password-protected websites, academic resources, and internal company systems. However, its close association with the more secretive dark web often leads to confusion.
This guide breaks down everything you need to know about the deep web, how it works, and why it plays a crucial role in today’s digital world.
The ideology of the deep web
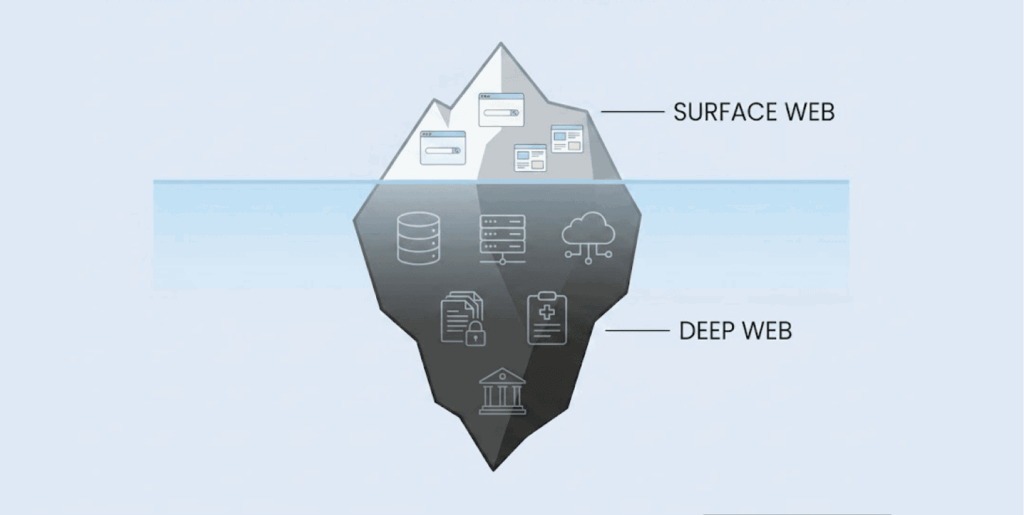
If there’s any content online that our traditional search engines (Yahoo, Bing, Google, etc) can’t index or find, the home of such content is the “deep web.”
Most often, we use the word “hidden” to describe it, and so many people think it’s dangerous or illegal. However, to put it simply, the deep web is a collection of web content and pages that one can access via special permissions, payment, or authentication.
Your Netflix account, Gmail Inbox, and that “MyOfficePortal” where you submit timesheets, are living on the deep web. Back in 2001, a Computer Scientist, Mike Bergman, came up with this term, and at the time, he roughly calculated that this hidden to be at least 500 times more voluminous than the surface web.
Even though the exact numbers are hard to determine, the deep web is beyond what a lot of people call “the internet.” According to security experts, what’s covering most of the deep web is the “walled gardens.” Call it secure areas that need permissions, subscriptions, and certain credentials.
To cut it short, it’s everything about security, privacy, and how legit institutions operate in the digital space.
How does the deep web work?
As stated earlier in this article, this space is all about privacy and security. So, how’s that done?
Through several mechanisms that hide sensitive content (especially) from appearing on our regular search engine. You’re probably wondering, what mechanisms can pull this off? It’s not rocket science!
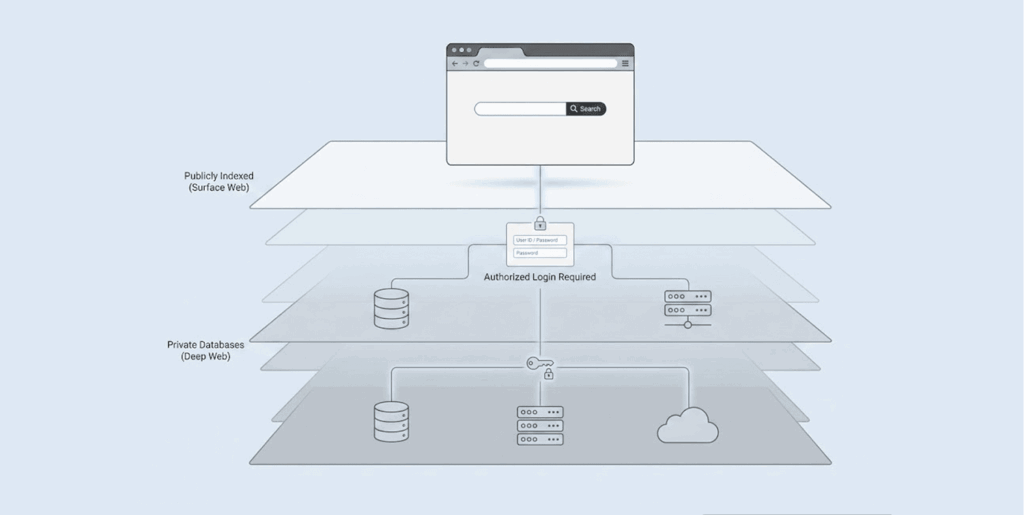
Authentication barrier
Login screens, access control, and paywalls: these systems hide sensitive deep web content. No matter the search engine in question, you can’t get past these or index what’s inside.
Each time you sign into your banking application, the pages before you are dynamically set up just for you. No replication or indexing by search engine crawlers gets to see what’s on those pages because they appear only when you’re “authenticated.”
Your social media DMs, email inbox, subscription to streaming services, and even cloud storage files work with this same system.
Technical limitations
Search engine crawlers, those little bots that scan the web, do a great job with regular web pages. But there’s a limit: they can’t handle everything. Give them a complex JavaScript site or a page that only shows up after you log in and click around, and they get stuck.
They don’t have the knowledge to fill out forms or carry out any action that will require them to take many steps or even find out the information they need. Due to their incapability, much useful information doesn’t appear when people search for them.
Robots.txt
Sometimes, websites want to be hidden. Admins will make sure the search engines don’t reach some pages by blocking them using tools like no-index tags or robots.txt files.
They are not trying to hide anything illegal but they only want to make sure that information that should be private remains so and doesn’t get into the hands of those it shouldn’t.
Dynamic content
Much of what people know as the deep web originates from dynamic content. These pages are not sitting there; instead, when you make a request for them, they’re made in response.
You can liken this process to when you want to check your bank account or make use of the internal system belonging to your company. Once you log in, the pages come up, but immediately you log out they disappear.
Search engines can’t do their indexing work on these pages because they’re not sitting still or available for the public to reach at any time.
Private networks
Content also exists on private networks or when you use different protocols. Some things need you to lay hands on special software, VPNs, or even direct network access just like what we know as corporate intranets.
The deep web can only work with server-side technology, connections that are encrypted, and access controls that are not available for all to use.
All these mysteries are not something to be shocked about. That space is there mainly to keep things private, and secure so that people who actually need the stuff there can lay their hands on them.
Everyone uses the deep web: Here’s how
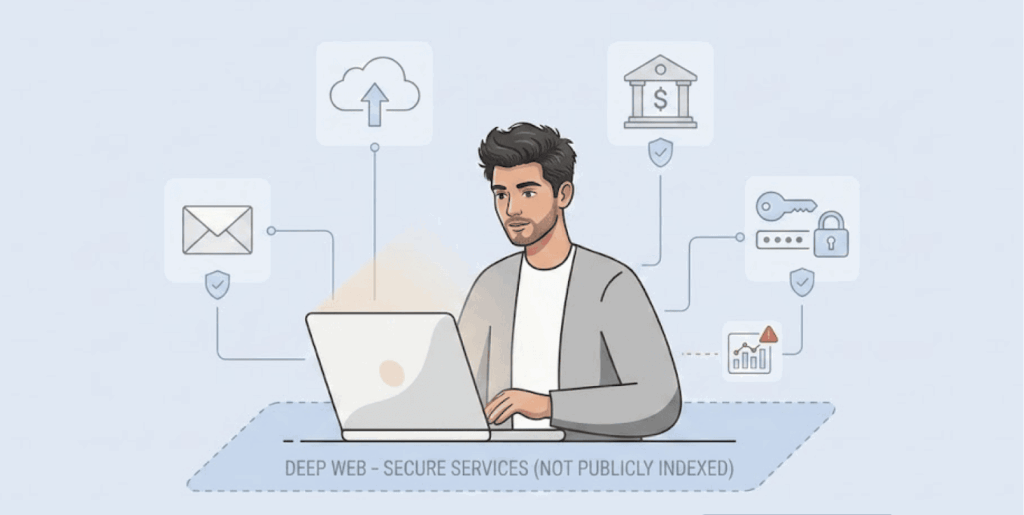
You might probably be wondering right now, “Am I part of the people using the deep web?” Of course, you use it all the time. Check some examples of how you are part of those visiting the deep web without even knowing you’re doing that.
1. Passworded
Any page that asks you to input some secret combinations (password) to open is part of the deep web you are hearing about.
For instance, your private messages on social media, logging in before completing your online banking, HR systems you find in different companies, the emails to send and receive, and even adding a password before opening your account on Netflix, they’re all behind passwords.
As soon as you add those private words or numbers and log in, you have just landed on the deep web. Search engines don’t have any way to get there because they don’t have your login info, and there’s a reason for that.
2. Intranets & private databases
Maybe you didn’t know before, large databases & intranets are also part of the deep web.
Do you know why data belonging to the government, University libraries, databases of companies databases, medical records belonging to patients, and files linked to the court files are all hidden away from public search? It is to make sure they are only open to the owners and that criminals don’t lay their hands on them and cause havoc.
Most papers you find are written after academic research, and special data usually appear here, and those who need it can only access them if they have the right login details.
3. Dynamic content
Pages that change depending on what you do are another example. When you search for airline tickets, get personalized suggestions, or view custom reports, those pages are temporary.
They appear just for you and then disappear. Google can’t index them since they don’t exist for anyone else.
4. Orphaned content
There are also pages on the deep web that don’t have inbound links. Some examples of the likes are drafts, temporary files, or old pages that have no connection to anything. If nothing at all linking to a page, there’s no way search engines will find it.
5. Paywalled content
Don’t forget about the contents you can only access when you make some payments. Academic journals, newspaper archives, & reports about industries are always only accessible when you pay.
Big-name newspapers such as “The New York Times” or “The Wall Street Journal” put much of their writeups and other content behind paywalls, so people only access them when they pay. Unless there’s a subscription form, the contents are invisible to both you and search engines.
6. P2P systems
Finally, some networks that are very private, overlay systems, and places where peer-to-peer sharing takes place are not seen on the visible web. If you must utilize more than a browser & a link before something opens up for you online, you’re already part of those using the deep web.
There is something you should bear in mind. The deep web is never this all secretive, and a world filled with shadowy creatures; it actually comprises some things you use all the time without noticing.
Now, have you not logged into Netflix to see the watchlist you created there? What about your Gmail and the many times you opened it? Have you ever checked your orders on Amazon or opened the library database belonging to your university to search for something?
If you have at one time done some or all of that, you have used the deep web. So you see, there’s nothing sketchy there. It’s just the part of the internet that keeps your personal info private and gives you customized content without making everything public.
The hidden internet: How big is it actually?
It’s bigger than you can begin to imagine. We’re talking numbers that you won’t think to mention and nobody really knows whether the developers blocked it from the usual search engines deliberately or not.
The best estimates we found stated that the deep web is somewhere between 400 & 5,000 times larger than the usual surface web. Billions & billions of pages, which are even getting bigger, are totally invisible to regular search engines.
Back in 2001, a researcher whose name wasMichael Bergman worked hard to decipher how big the deep web was to no avail, but instead he could only guess that it is 500X bigger than the web we use daily surface web.
At that time, when he tried this search, the number of documents search engines indexed was just about a billion, but the deep web contained more than 550 billion. That’s shocking, we know. Anyway, search engines are no longer that low, although the deep web is still topping the charts, of course.
What makes up a larger part of the deep web includes the databases and accounts we use, such as all Facebook profiles online, bank transactions, Amazon listings, etc. To make everything easier to understand, DataReportal says 5.41 billion people, about two-thirds of everyone on earth makes use of social media.
Another important piece of information from researchers is that the number of emails people all over the world send in a day is about 376 billion. That’s enough for every person in the world to get 47 emails on a daily basis.
All those emails you send & receive, the attachments that follow them, and conversations we usually have with others on certain online pages are all contents belonging to the deep web. Let’s not forget the tax documents, all the pictures, and some places like iCloud, Dropbox, or even the popular Google Drive that houses your creative work.
Those things are not visible on the public search engines but they are still somewhere online for you, and also consuming their own space.
What’s driving this growth? Accounts locked with passwords, databases belonging to the government and other corporate organizations, and other contents that need you to make a request, cloud storage where your files hide in, and paywalled sites, plus people’s need to have slim privacy, are all causing the growth we see around the deep web.
As more people get concerned about their privacy, the more their belongings (content) end up behind logins.
Deep web myths and truth: What’s real?
Is the deep web dangerous?
Many people really believe it is dangerous but that is not the truth. Most of what goes on there is just the normal things such as housing your email, your bank account, the tools you work with online tools, and the streaming services you pay for.
There is nothing dangerous about all that; they’re just private. If you use strong passwords and connections that are secure, you won’t face more risk using the deep web than reading the news online.
In fact, it’s sometimes even safer, since it protects and hides everything personal about you (your information) from the public. Of a truth, risks exist online but not everywhere. Just like anywhere else on the internet, some areas of the deep web pose some dangers, too.
But most of those problems usually crop up around certain spots, especially in relation to the dark web, not everywhere on the deep web.
Unfortunately, a lot of people don’t know this because the news stories they read or hear usually focus on highlighting the activities going on on the illegal markets, forums for hackers and all those other things that can scare anyone.
But honestly, those stories are mainly talking about the dark web, not the entirety of the deep web. It’s like saying that every building around you is dangerous just because something bad took place in one questionable warehouse.
Why do people mix things up
Most of the fear people express about the deep web is due to the nefarious activities going on on the dark web, and only because they’re confusing one for the other.
Big headlines all over the place relating to cybercrime, dangerous deals around drugs and incidents of hacking usually make people think that, as long as something is hidden, drug deals, and hacking make it seem like anything “hidden” from Google must be shady.
But that’s not how it works. Almost everything you can’t find when you do the normal search is hidden for very good reasons, like to keep people’s information private and secure so that criminals don’t use them for evil deals.
What are the actual security risks?
The real risks present on the deep web are still like the ones present on the regular internet we use. Don’t forget issues like social engineering, scamming attempts, and malware infestation, or even the popular phishing emails, are also present on the surface web.
The only difference you could mention is that criminals on the deep web might really know advanced ways of achieving their intentions on specific targets. On the other hand, big organizations sometimes use the tools on the deep web to keep their details and operations even more secure.
Have you heard about private networks, databases with encryption, systems you can only access with passwords are usually better off on the deep web than to be kept where everyone can access the information they house.
Keeping things in perspective
The truth is that problems only arise when you go searching for something you know is suspicious or against the law.
You won’t stumble onto something dangerous if you only check the messages in your email or log into your account with the bank, even though those activities technically take place on the hidden web.
In fact, carrying out your banking activities via portals that are secure portals is better and safer than opening any site you come across on the regular internet space. If you keep opening sites that you don’t know, cybercriminals might get you with malware onto your device at the time or scam some of your money on one of those sites.
Surface web vs. deep web: What’s really going on?
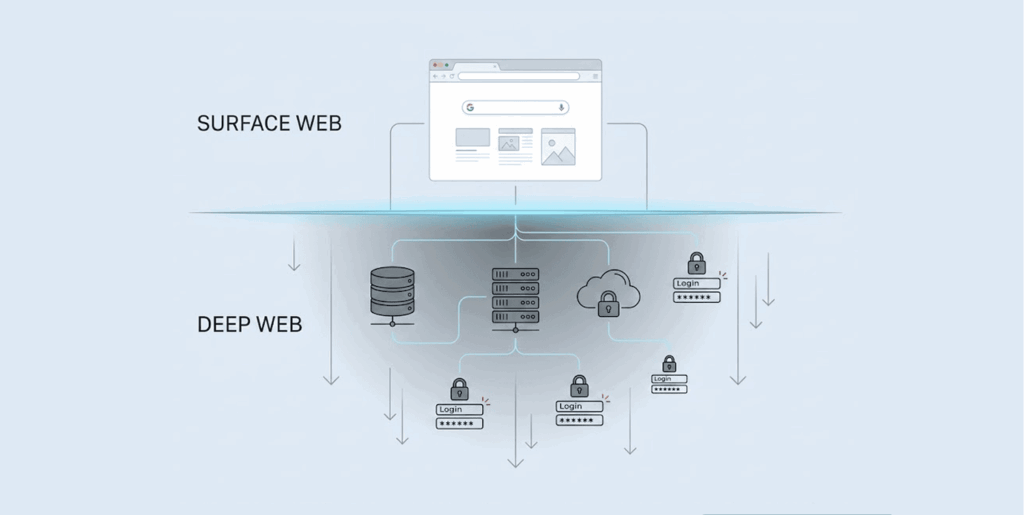
Imagine Google as a VIP event where attendance must be based on having an invitation to it, which, of course, must come from those who own websites and allow search engines to enter their pages to index them. Here’s what actually happens:
How pages show up on the surface web
First, someone creates something online which could be a blog, a store online, or even a simple video, etc., and it sits on a web server, and anyone that knows the address can actually reach it.
Next, the site owner calls the search engines in through sending what is known as a “Sitemap” or just following the standard web practices. This is their simplest way to tell Google to look at the site.
Then, bots like Googlebot move up and down the site, examining the links and looking at what’s there. Afterwards, search engines add what they find to a giant “index”. This is like a kind of online library that houses billions of pages.
When you visit a site and search for something, the search engine checks this giant index & brings up the public pages that match your query. In this regard, if website owners don’t take the steps above, any content they post stays hidden from people’s eyes.
Why do deep websites hide on purpose?
Here’s the real scenario to note: every site owner is in full control of what happens on their pages, to be indexed or not. As for the part of the deep web sites, they just choose to stay hidden to all except the owners.
They don’t send out sitemaps, they block whatsoever bots with tools like robots.txt, or they put everything behind a login. It’s not like something random; it is something intentional.
Why keep things private?
The reason for keeping things as they are is to make sure the things they house remain secure and private to the owners alone. Consider some things, such as your bank accounts or medical records. Would you want everyone to know what’s inside them, or would you want everyone to use your subscription on Netflix freely while you paid for it? That would be simply chaotic.
Hiding important things keeps the owners private and not to be exploited because everyone knows everything about them. Nobody wants the public to be able to mention their credit card numbers, know the details of their health status or know the messages they sent or received from others.
And this privacy is not only for regular people but for businesses and government institutions too. What about people who offer their products based on subscriptions? They wouldn’t want their systems to be open to the public, but to those who actually need and make payments for them. All that is why the deep web is there to keep that sensitive information from becoming ubiquitous but instead useful to the right people.
Another important thing the deep web makes private is intellectual property. Some places where you can find academic research are not free for anyone to access. Anyone needing anything from the over a million papers there will register first, so the copyrights will remain safe and not appear on public search.
Now, let’s make a comparison between the deep web and the dark web, because many people don’t know that they’re different. This confusion confuses them and leads them to fear what is not as bad as the sound. The truth is that both places are different and their work is also different. Moreover, the way you reach them and what you will find in them are also different.
Deep web vs dark web: What’s the difference?
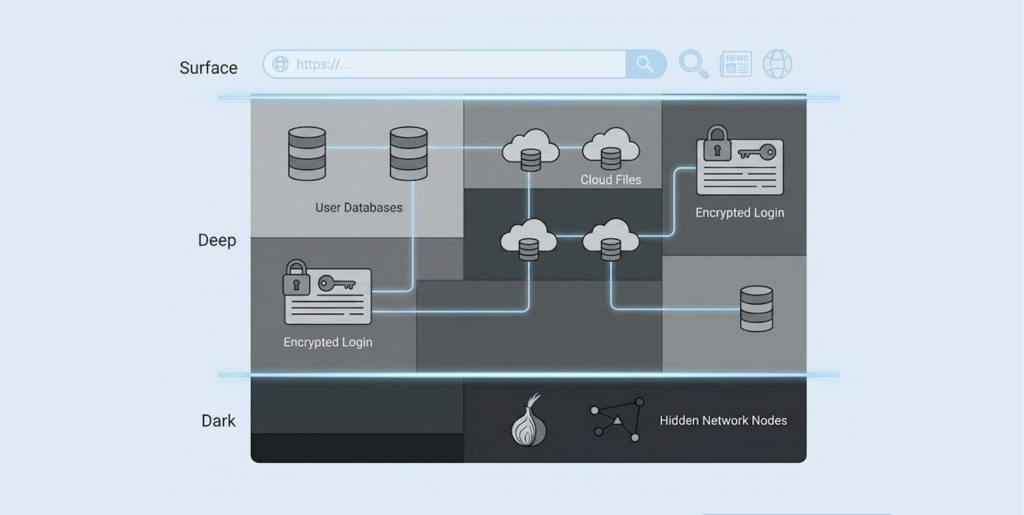
The simple way to describe the deep web for you is that it is those things that you can’t find with the search engines.
Now let’s mention them. Can you find your email inbox when you search on Google? There is no way. What about the databases belonging to any company or those websites that demand payment (subscription) before enjoying what they have? In fact, anything you must log in to find or pay to reach is inside the deep web.
Almost everything hiding in the deep web is legal and just some standard stuff. You use it all the time, without knowing or even thinking anything about it. Now, inside the deep web is another hidden place called the dark web, and it is a much smaller, really private area that you can’t just use a search engine like Chrome to reach.
To venture into this space, you must have a special tool like the popular Tor browser which will take you to some sites that have “.onion” addresses. The thing described above is all to make sure everything there is private, those who go there remain anonymous, and content there comes with encryption while the traffic is rerouted to avoid surveilling eyes.
Yes, the dark web is popular for permitting activities that are against the law to take place, such as housing the black markets, supporting the buying and selling of stolen goods, etc.
But there’s more that happens in that space than what we think. Apart from criminals, journalists, activists, and most ordinary people whose governments are so keen on hiding information or surveilling their citizens, use the dark web to avoid all that. So, it’s a crucial platform where many go to gather important resources.
Now, let’s create a simple example to make the difference sink in. Now imagine that the internet is a city, the surface web you are using everyday are those main streets, shops, even restaurants, and all those other places you see around.
On the other hand, the deep web is like those houses, office buildings or every other space you can’t enter except when you receive an invitation or book an appointment.
The dark web? Yes, think of that space as those underground bars, fighting rings, and gambling dens that operate in some basements. They’re there, but very small when you compare them to the other spaces. Getting into each one is different.
If you want to enter the deep web, you just need to open a browser, for instance Chrome, Firefox, Safari, etc then you add the correct details to log into the deep web space.
The dark web, in its own style, needs you to do more than that. First, the Tor browser must be your pathway, and there must be 12P or Freenet. The reason you need these is to make sure nobody finds out that you entered the dark web, especially the government. So these tools will shield you and your movements there. The types of content you’ll find are different as well.
The deep web is a house for everything that is legal, which the owners wouldn’t want others to see because it is private to them. Some of those things are legal files, medical records of a patient, subscription to certain services, emails, and databases belonging to businesses.
On the other end is the dark web, where people go to buy different illegal things. You will find privacy tools, dropboxes of whistleblowers, tools for committing online fraud, sketchy forums, and chat rooms where people discuss anonymously. It is hard to predict what’s going to happen in that space, and people go to these places for different reasons, too.
People using the Deep web just do ordinary things, like when they check their emails, log into the company platform to work, complete their transactions on their banking platforms or simply stream their special shows.
Those who use the Dark web are after being completely anonymous. Sometimes they do some good things like fighting against half-truths, protecting the people who expose the truth or simply staying private. But other times, a lot of illegal things take people to that place.
Here’s a quick summary:
| Feature | Deep web | Dark web |
|---|---|---|
| What it is | How do you get in | Content search engines won’t access; there must be a login, paywall, or credentials. |
| How you get in | Why is it still in existence? | You must use Tor, the tool for communication, I2P, or a network known as Freenet. |
| Why is it still in existence | Every day browsers can do the trick, can let you access. Like Chrome, Firefox, and Safari. | Some of the activities are lawful, but much of everything else is illegal. |
| How big | There must be Tor, the tool for communication, I2P, or a network known as Freenet. | A small size that doesn’t take up much of the deep web. |
| What’s there | Almost everything taking place there is by the side of the law and is really important. | Forums that are hidden, the markets where illegal things are sold and places where whistleblowers reveal information. |
| Legality | To keep things Private and secure during everyday usage. | Forums that are hidden, the markets where illegal things are sold, and places where whistleblowers reveal information. |
Note: For a curated list of popular dark web sites you can visit once you have Tor, check out our guide to the best dark web sites.
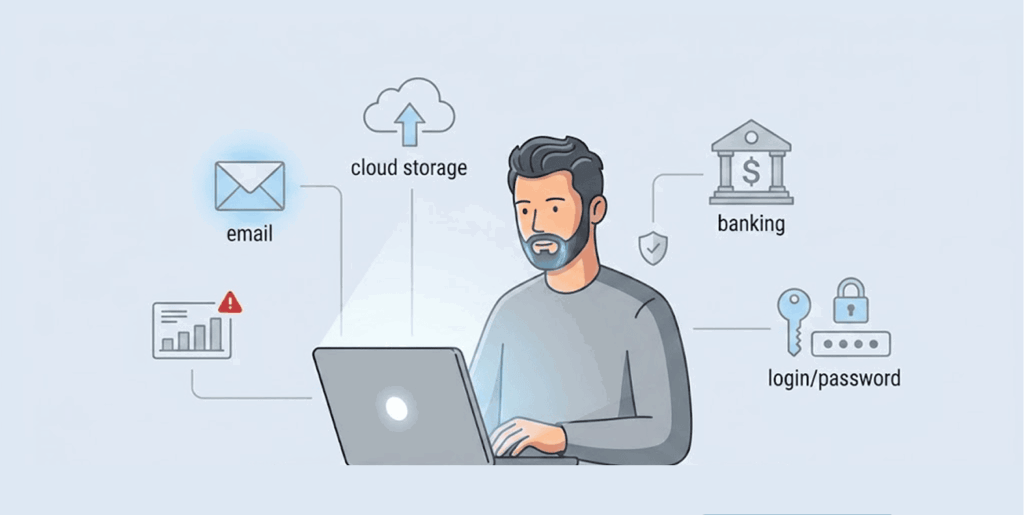
How to access the deep web and why you already do
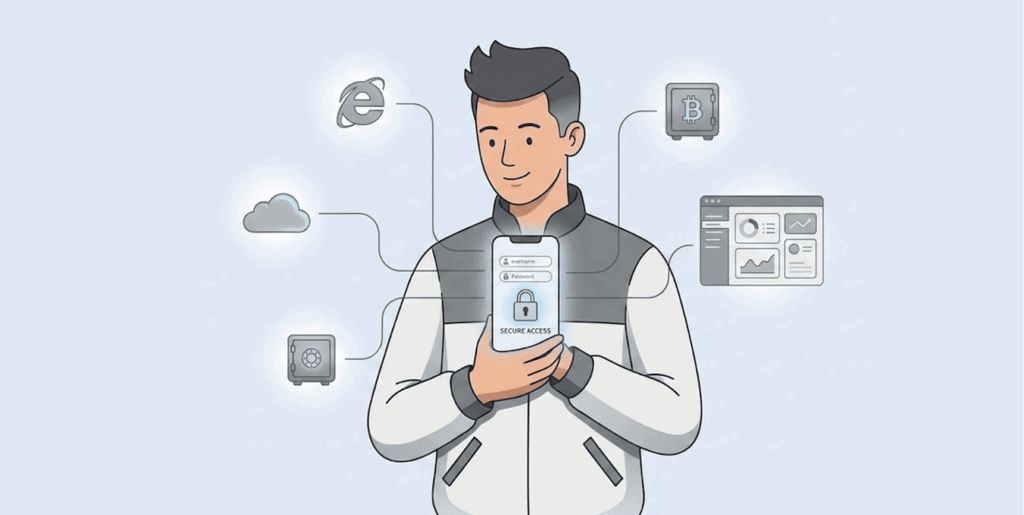
All anyone needs to reach the deep web is to have the right address pertaining to anything there and then use your own permission codes login details.
For example, when you want to check your email and first visit https://mail.google.com, you have gone inside the deep web. If you also open your bank site and do one or two things, that’s you on the deep web.
All you started with was just to put in the name you registered there with username and the numbers or characters which only you know (password), then the browser you entered the whole thing into will link you to the server, and those things you entered will be checked if correct or not. If correct, you will have your account or inbox open, but if they are not correct, the reverse becomes the case.
All those things that are supposed to be private, like your emails or your bank records, are hiding in the deep web. Search engines don’t have the right or the permission to index them because they are hidden, but only because they’re not for public consumption.
It all uses the same “standard internet protocols” like the popular HTTP & HTTPS but more security is there because even the owner must authenticate their ownership. If you want to enter further inside the deep web (legally), you can visit some other areas that are purely legitimate, you can visit without breaking any laws.
For example, you already know that Universities have academic databases & digital libraries that house many research reports, there are archives, and more. Sometimes, once you get a library card or sign up with your information, you can own a free account to access and reach those things.
Now there are other fields such as law, medicine, and finance that also own databases in the deep web where they store special content. Sometimes, to get those contents, you must make payments to become a member, or you can check if there’s a free way to use them or a trial period without payment.
Further, many government agencies have millions of records belonging to the public records, and some could be court documents, & statistics in databases where you can search easily on the deep web. These are usually free, but you’ll need to know which agency is responsible for what you want.
There are even search engines that are mainly used to enter the deep web and some of them are Pipl, TinEye, or Yippy. These ones can find the things Google can’t because they search different places behind the scenes.
What happened to Silk Road? The rise and fall explained
The original place bearing “Silk Road,” which maybe you have heard of over the internet, was a popular marketplace amongst criminals on the dark web.
People went there when it was open to buy and sell anything illegal, which might be drugs, fake documents, and other things you don’t want to hear. It was going on strong until October 2013, when the FBI pushed it out of that space.
The agents arrested Ross Ulbricht, the person in charge of the site going by the name “Dread Pirate Roberts” online. Now he is serving a life sentence with no provision for parole. But after the closing of the market, other bad actors emerged and created other markets like it, calling them Silk Road 2.0, 3.0, and others, all in the bid to enjoy the popularity of the first market.
Even as they kept creating more markets, law enforcement continued to chase them, closing down new markets as they cropped up, creating a tug-of-war scenario.
Now, there’s nowhere to find any real “Silk Road” anymore. Most sites that cropped up as its successors are just there to steal crypto assets from users. Also, the authorities are using such appearances of silk road to trap criminals.
Occasionally, a new site will crop up in the name of Silk Road, but the authorities take it down very fast, causing the operators and users of the site to move onto other markets with different names and designs.
So what replaced it? Many new markets have started operating, coming up with different rules and measures to secure their users. But some usually die off fast after running away with people’s money in an escrow exit scam or are taken down by law enforcement agencies even after staying for years.
Law enforcement has become even more knowledgeable at catching the dark market operators and closing the sites down. Agencies like the FBI, DEA, & Europol have devised their own means of entering these sites, and fishing out those who operate them, and even follow traces of transactions completed in cryptocurrency.
The takedowns of AlphaBay & Hansa Market in 2017 is proof that as far as a market is illegal, it is not safe in the eyes of the law, no matter how advanced their security tools appear to be.
There is something you should also know if you want to venture into the dark side: a mere visit to such places can land you in trouble with the law, and you pay dearly for that. It doesn’t matter whether you bought anything or not.
Law enforcement are always watching these sites closely, and they really track those who even pay visits no matter how deep you must have hidden your activities.
For ordinary users, knowing if their own data appears on these monitoring sites is equally important. Google’s dark web report tool, which provided free breach alerts, has been shut down, forcing users to turn to alternative monitoring solutions to stay informed about whether their personal information has been compromised and is circulating on dark web forums.
Top pick for deep web privacy: NordVPN
If you want to take a further step to ensure your privacy on the deep web, NordVPN is a tool you don’t want to miss. Its work is not only hiding your IP address but also covers you from many threats.
One feature that stands out in this VPN is the servers it uses to route your traffic directly through the Tor network. This means you don’t need another layer to remain anonymous when using TOR. On top of that, it makes sure annoying ads and trackers, or suspicious sites, don’t use or grab your data.
NordVPN also monitors the dark web on your behalf to make sure that your data is not appearing in places where it shouldn’t. But if it finds that your details appeared on any leak site or dark market forums, it will send you an alert so you can take action immediately.
That way, you can immediately change your password and prevent any hijacking attempt on your account. The service respects people’s privacy by not logging their data, meaning that whatever you do online doesn’t have a record anywhere.
The best part is that a quality VPN such as NordVPN will hide your activity so that even your internet provider won’t know what you are doing. As for crossing over firewalls to access something, this VPN helps you with that and hides your browsing activities with its obfuscated servers, making the traffic look like normal HTTPS traffic.
This is a help you need, especially if your country censors information or when you want to hide well from surveillance.
Steps to open .onion sites with Tor
We’d mentioned that if you want to open .onion sites (which are dark web websites), you need special tools like the Tor Browser.
So, now, let’s show you how to access the websites using Tor, whereas our regular browsers can’t open them:
- Get the Tor browser only from torproject.org.
- Do as the instructions on the screen say to install it.
- Launch the browser after it’s installed, configure it, and click on “Connect.”
- If you have any .onion links like this bbcnewsv2vjtpsuy.onion, copy and paste them into the search bar and start browsing.
- Visit legit directories like OnionWiki.com, Dark.Fail, or Tor.Dog to find uses .onion links.
To discover more .onion sites beyond these directories, check out our list of the best dark web search engines, which can help you find everything from privacy-focused forums to legitimate research resources on the dark web.
Tor safety tips
- Set the security level of the browser to “Safest” to remove JavaScript and other risky scripts.
- Never use your real information on Tor; this means avoid even your email or social media.
- Always scan documents and attachments first before getting them into your computer. Do everything possible to stay safe.
Staying secure on the deep web

The deep web is not there to grab you or land you in trouble because even the surface web still has some risks when you use it. Still, doing all you can to stay secure in the digital world is not a bad practice no matter what you are doing there. So, try the steps we have below to protect yourself whenever you visit those sites.
1. Good security habits
Make sure the same password is not what you use on all the accounts you have online. Every service you are making use of must get a new and of course strong password for entering it. Don’t ever make it simple, but let it be complicated so that no other person can easily guess it.
Using a password manager is something you should actually think about because they are there to create very strong ones for you and even store them so you can use them when in need. Another habit is to always keep your two-factor authentication enabled so that it will come into play for more serious accounts like your email, bank, or work.
Most importantly, don’t be lazy to create a new password from time to time, and when you notice that someone has entered your account, change the password.
2. Protecting your devices
There are important devices you use to access the deep web that you must keep up to date against cybercriminals. Some of them include the operating system of your device, the browser, and the antivirus software you use. The reason for that is to prevent cyberattacks because of software that has become outdated & easy to infiltrate.
Even if all you do is check email, make sure to have an antivirus protecting the device and your email. If you even go closer to the dark web, expect more dangerous threats, & if there is an antivirus, it will cover you from bad actors.
Now to further handle things better, make sure that you adjust the security settings of your browser. Turn off any plugin that is not useful and download the blocking software against ads and use a browser that functions to protect its users by maintaining their privacy while online.
3. Smart browsing practices
Don’t use your private login details randomly on every site because criminals spread phishing pages everywhere, and they win when people make mistakes. The shortest way to be careful is to check if you’ll find the padlock icon in the address bar of your browser before entering any personal information.
That icon means that the connection is with encryption, and as such, fraudsters can’t easily grab your data. Also, any message or email that comes asking for your personal information or demanding you enter your password, don’t do such even when they seem to be legit.
Scammers are improving their antics every day. So make sure you find out who sent the message and don’t click on any link that appears before you find yourself on a scammer’s site. Businesses that are genuine will not demand that you share your sensitive information or password for anything.
As for files that come with emails, never download them unless the source is legit, because scammers hide malware in those downloads to hijack your system through malware.
4. Consider a VPN for extra privacy
If you want to check your email or bank accounts on the deep web, using a VPN is not compulsory. However, if you are checking these things on a public network, you must want more privacy, making a strong VPN such a good idea.
Therefore, try getting a VPN service that has a reliable encryption system and also protects your network from IP leaks. Further, a service that doesn’t log your data and still offers you speed is a good one too.
5. Guard your personal information
When on the deep web, make sure that you guard your personal information jealously and only make it available only when you must, especially for those services that you can only access by providing more personal data.
But before doing that, check their privacy policies & data handling practices especially if the data you will share is very sensitive and even relates to your funds.
Don’t just stop there. Be checking your accounts more often so you can notice when unusual things take place there. Don’t ignore your credit card statements or your bank account for too long.
6. Understand your legal limits
Many people usually ignore the terms of service on deep websites. Don’t do that, please. Try to read them so you can avoid violating them and facing legal issues. Make sure you don’t engage in any illegal or questionable activities, and you can do that by trusting your instincts sometimes.
Also, if the content is not your original piece, avoid the temptation to share it. Much of what you find online is under copyrights and if you share without getting the right permission, you will land in legal trouble. Sometimes the problem here is not the deep web but the inability of the users to take security seriously.
Conclusion
The deep web isn’t some mysterious digital underworld. Now you know, it’s simply the content that you use every day that you put a password on.
People still confuse the deep web with the dark web. Again, you’ve seen the differences as broken down in this guide. Just do the basics, use good passwords, update your software, and guard your personal credentials.
And consider learning about dark web monitoring, a proactive security measure that scans hidden forums and breach databases for your personal information, alerting you the moment your data appears so you can take action before criminals use it for fraud or identity theft.


